Recent news stories about the security breaches and hacking of major corporations IT systems have made some in the IT field question the security of cloud services. For a while, these high profile cases seemed to have dampened its bright future but the cloud companies have bounced back with their swift response to the issues to restore the trust and confidence of enterprise users. The companies providing cloud services understand the severity of the issue more than anybody else. They are convincing their customers by bolstering the security around the cloud without wasting any time. The users are also so eager to know what the cloud providers are offering them in terms of security.

Cloud strategy and assessment workshop
The adoption of cloud-based infrastructure by enterprises is increasing greatly. However, a lot of enterprises are still reluctant to adopt a cloud strategy due to lack of skills or knowledge.
As we know, enterprises have already realized the potential benefits of adopting cloud services. Fortunately, cloud computing system has evolved as highly capable and compatible to solve the existing vulnerabilities. As a result, enterprises are convinced now and become more enthusiastic to embrace it. Now the only thing they should focus on is the selection of a cloud partner which is pretty much critical. They should find a company that has an impressive security model in place to keep the entire cloud things safe and secure for them.
A study by Gartner considered Cloud Computing as the first among the top 10 most important technologies and with a better prospect in successive years by companies and organizations- Gartner identifies the Top 10 strategic technologies for 2011.
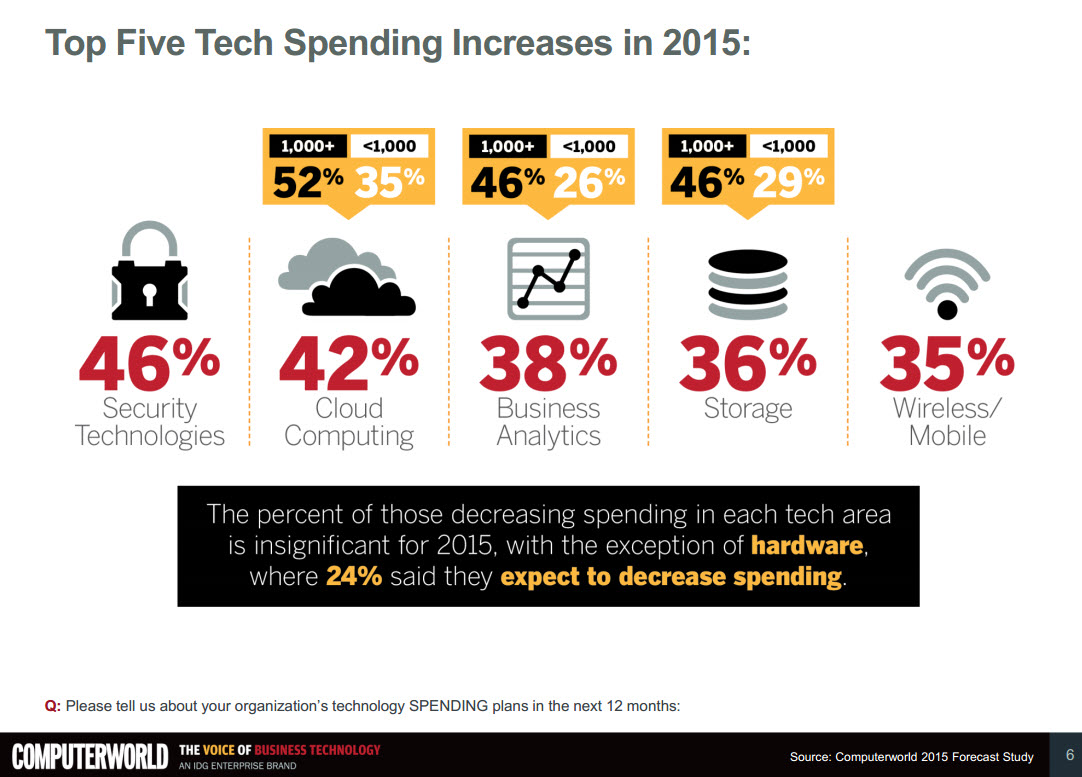
Noticeably, there is a huge rise in enterprise IT spending in recent times and we can see that a fairly a big sum is going to cloud computing and tech security. Such realities make everybody pay attention to cloud services and its smooth operations. The main market players like Amazon, Google, Microsoft, Rackspace, VMware, IBM, HP, Alert Logic, etc. are spending a lot of resources and time on cloud security features which brings a sense of positivity to the entire cloud world. Enterprises themselves are allocating time and resources to secure their data as much as possible.
Taking Measures Against Vulnerabilities
Though there are apprehensions regarding the cloud computing, people are showing patience toward it as they know any young technology could have gone through this phase of uncertainties in its nascent stage. Moreover, there are many measures both enterprises and the service providers can take to make cloud computing secure. We must have a cloud environment that ensures confidence to run our applications just as the way we would run them on our on-site setup. As we do not want to get into any data leakage, we need to find ways to eliminate security threats that are lurking around the cloud.
Choosing your right cloud partner
It does not seem to be an easy task because at first people are likely clueless as to who can provide the best security. We should consider choosing a cloud service platform which can be integrated well with our existing IT mechanism. Selecting an established cloud service provider is much more advisable because this is comparatively a road less traveled and it is not necessary that a newcomer can take care of all the vulnerabilities lying ahead of it.
Protection at hardware level
Enabling an infrastructure, which is more reliable and supports compliance, is something very crucial. Taking measures to protect the server location and taking control of the environment should not be overlooked. The hardware level protection must to build up trust and compliance to the data center infrastructure and endpoint users. You should essentially create protection into the hardware to secure your software better.
Encryption
The most accepted and widely practiced method to protect data is encryption. This is the best practice which ensures security against loss of physical control of your data. With the data is moving out of the office premises and causing vulnerabilities, this method can be effective. Especially when your data is in the cloud, encrypting data ensures non-readability to unauthorized users.
Protecting client/server platforms
With the increasing level of malware attacks, safeguarding the client and server platforms is considered one of the most important security practices. By doing this, it establishes trust between servers and client platforms. It demands smart controlling of software layers including firmware and hypervisor virtualization layers. This reduces the risk of intrusion by a remote or virtualized infrastructure.
Establish secure cloud access across life cycle
Solutions like Cloud Identity Manager and Single Sign On are considered as one of the unavoidable solutions to provide secure access to the cloud data. The process involves sturdy safety standards including one time passwords (OTP) and using application web service protocols such as REST, SOAP, or JASON etc. Following these measures would ensure a great deal of security for the applications and data in the cloud.
Keep your applications safe
Keep applications safe by practicing some established methods such as using strong authentication tools, creating a threat model for applications, preparing for vulnerabilities in shared models, implementing SSO or identity federation solutions, activating DDoS (distributed denial of service), data loss precautions, protecting data privacy, and maintaining governance etc.
There are many more solutions emerging to secure cloud computing. This is comparatively a new technology and things are going to be more infallible in the coming years. The underpinning aspect of our argument regarding cloud security is that we as users too should be conscious about the security gaps that disturb the cloud computing. Our ability to stay ahead of these gaps also depends on having a sturdy IT establishment on our own. As the tech world has already been engaged in understanding the vulnerabilities and finding solutions for them, we can say that the future of the cloud is going to be a thriving business that can go the distance!