Customer background
Our client is a financial services provider that enables touchless payment options. The company is based in Canada and offers its products across the globe. It offers NFC-enabled wireless receiver that allows for instant acceptance of any contactless payments.
Challenges
The client has several NFC-based wireless devices that allow charity event attendees to donate with a single tap. Although, different credit and debit cards mean different payment processors. Hence, the data transfer between the card tapped and the server must be secure and received by the respective processor.
If the donor has a Visa card, the information should be transferred and matched with the Visa payment processor. It was challenging to secure confidential information and share it with the respective processor simultaneously. This also requires a thorough tracking of each touchless payment device for better visibility into each transaction.
The company had software that shared the device details and allowed the employees to manage orders. However, it was built on monolithic architecture. The application was not scalable and required more deployment and restart time. Also, the cost to maintain the application was very high.
- Security concerns
- Lack of visibility of the transactions
- Insufficient device tracking
- Monolithic architecture
- Costly and time-consuming software maintenance
Solutions
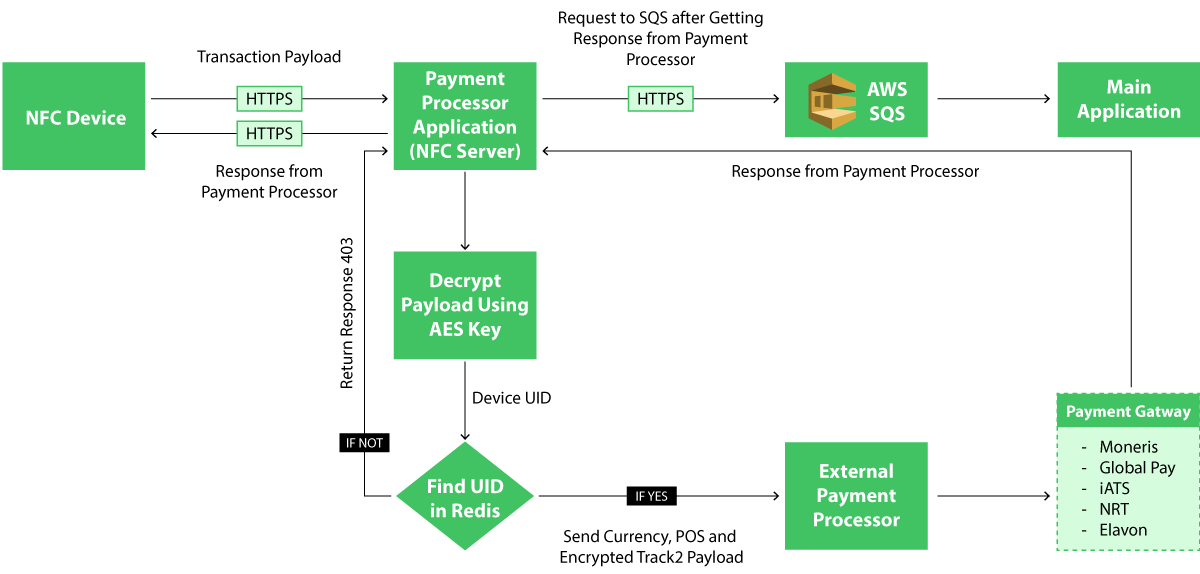
It was important to get an in-depth knowledge of the business model of our client to provide best-in-class solutions that can efficiently address their challenges. While dealing with financial data, it is crucial to secure the transactions to avoid fraud. Understanding the criticality of this matter, adept data experts at Softweb Solutions suggested implementing an intermediate server. Our solution allows the company to transfer data securely from their device to the relevant payment processor.
Intermediate servers
The company can now securely share encrypted confidential data with the bank servers. The data is transferred to the relevant payment processor without any delay or corruption in an acceptable format (for example: CVV, expiry data, etc.). The data is encrypted using the AED algorithm. Our data consultants leveraged AWS HSM as a security token that can be generated to secure the communication between the NFT device and payment processor. One processor has one related physical HSM key that is accessed by only one authoritative person from the company.
Customer-facing app
We developed an interactive web portal that can be accessed by the employees as well as their customers. Employees can leverage the app for efficient sales-order management. They can get orders, review them and accordingly share a quote with clients. Customers can customize their purchase orders from the web app. The company can also track the devices that the clients use to gauge data on the amount received from each of the devices, they can also activate or deactivate the device remotely, depending on the requirement of the customer.
Previously, the app was built with fewer features using monolithic architecture. We rearchitected using microservices. Our team of developers leveraged the DevOps methodology to divide the app into containers that can be easily managed and updated separately without hindering the working of other modules. This allows the comapny to scale the application and save time and money while updating the app or adding new features.
Third-party audit
To adhere to PCI compliance, we offered a security assessment to ensure all payment card information is handled securely. We also involved third-party and payment gateway partners in the process. After a thorough security assessment, the company became PCI DSS compliant.
- 95%
Improved security
- 100%
Device visibility
- 85%
Enhanced customer satisfaction
Improved security
-
Industry
-
Technologies / Platforms / Frameworks
Java Spring Boot, AWS, Spring MVC, Thymeleaf, JUnit
Decades of Trust & Experience
1630+
Projects
545+
Experts
26+
Products and Solutions
1020+
Customers
Similar Case Studies
Connect Now
Our experts would be eager to hear you.



